This is my very first post after I switched to www.kwokhau.com and this is also my very first time setup Azure RMS and SharePoint 2013 IRM integration. :)
I have an Azure RMS connector installed in my environment, hence I won’t cover the Azure RMS connector installation. I used the Azure RMS connector for File Server protection, and it is working fine.
First thing first, I launched Microsoft Rights Management connector administration tool and added the SharePoint server and the SharePoint service account to the list.

Note: I missed the SharePoint service account and I got the error below when I configure the IRM in SharePoint. Please remember to add the service account as well.
“The required Active Directory Rights Management Service Client (MSIPC.DLL) is present but could not be configured properly. IRM will not work until the client is configured properly.”

After added the SharePoint servers and service account, go to your SharePoint servers (Front-end SharePoint webservers, including those hosting the Central Administration server) and install the MSIPC client, it is available to download from https://www.microsoft.com/download/details.aspx?id=38396
After the installation, browse to Program Files\Active Directory Rights Management Services Client 2.1 and check the msipc.dll, make sure it is 1.0.2004.0 or later.

Next, run the GenConnectorConfig.ps1, the powershell script is together when you download the RMS Connector from https://www.microsoft.com/en-us/download/details.aspx?id=40839
Run PowerShell as Administrator and run the script, change the URL to your RMSConnector URL ".\GenConnectorConfig.ps1 -ConnectorUri https://rmsconnector.contoso.com –SetSharePoint2013"

The script actually helps you to configure some registry settings listed in https://docs.microsoft.com/en-us/information-protection/deploy-use/rms-connector-registry-settings. You can crosscheck and double confirm after run the script.
Okay, the configuration of Azure RMS Connector for SharePoint 2013 is done. Next is to enable the SharePoint IRM and then configure the Library Setting IRM.
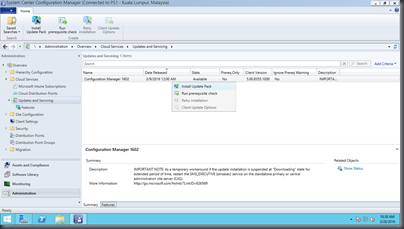
Go to your SharePoint 2013 Central Administration, Security, and then click on the Configure information rights management.

Click Use this RMS Server: and enter your RMS connector URL, and then click OK.

Now, you can start configuring your Library Settings IRM



Configure the IRM settings above as per your requirements and then click OK. Upload some document (without RMS protected) to see the effect. Then you can try upload some RMS protected document to see the differences. HAVE FUN!!!